IPA Web UI 配置账户
通过Web UI 配置账户
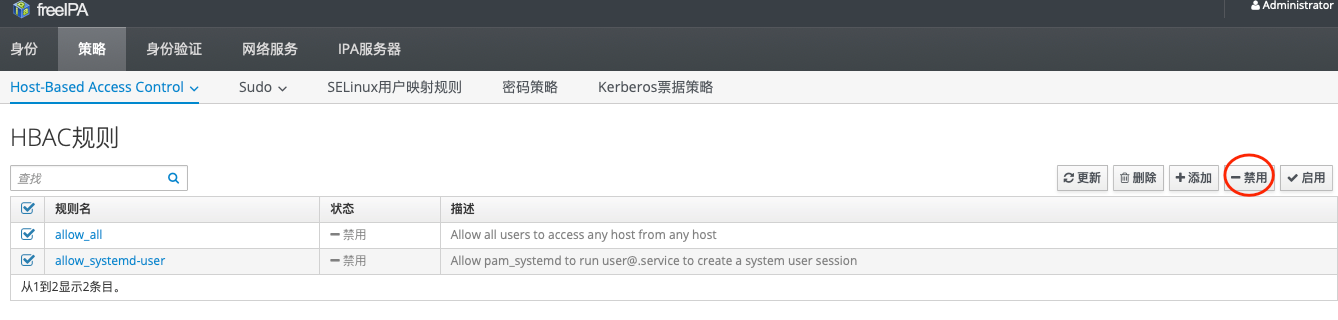
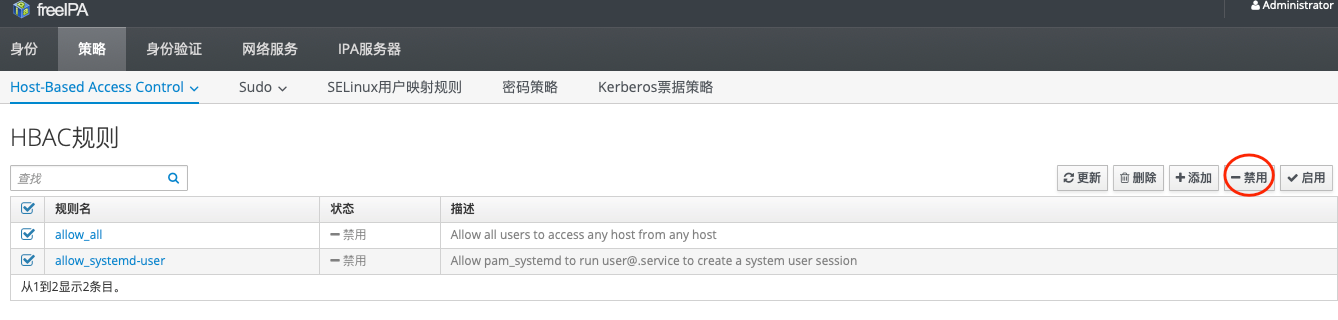
1、先禁用HBAC的两条规则
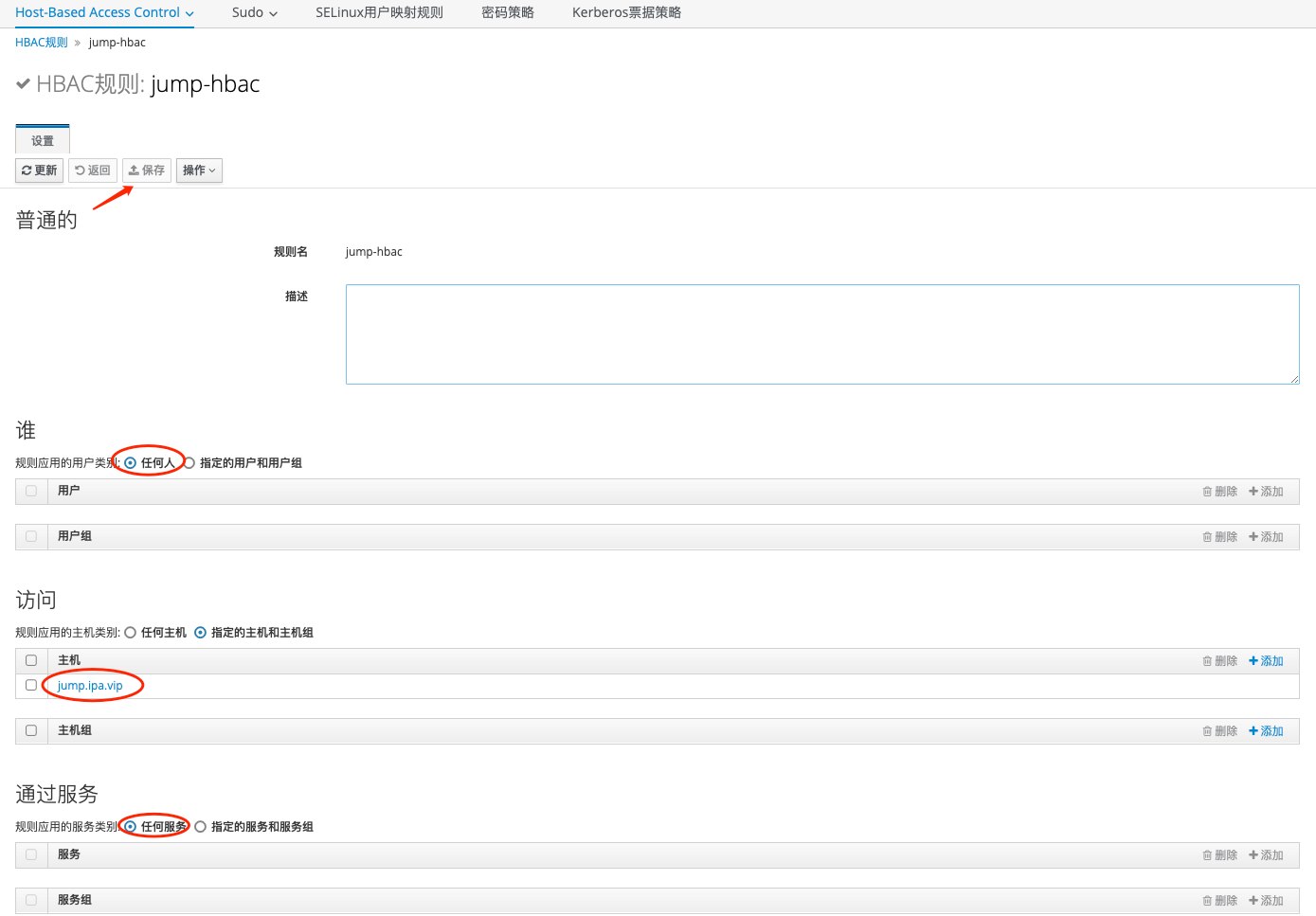
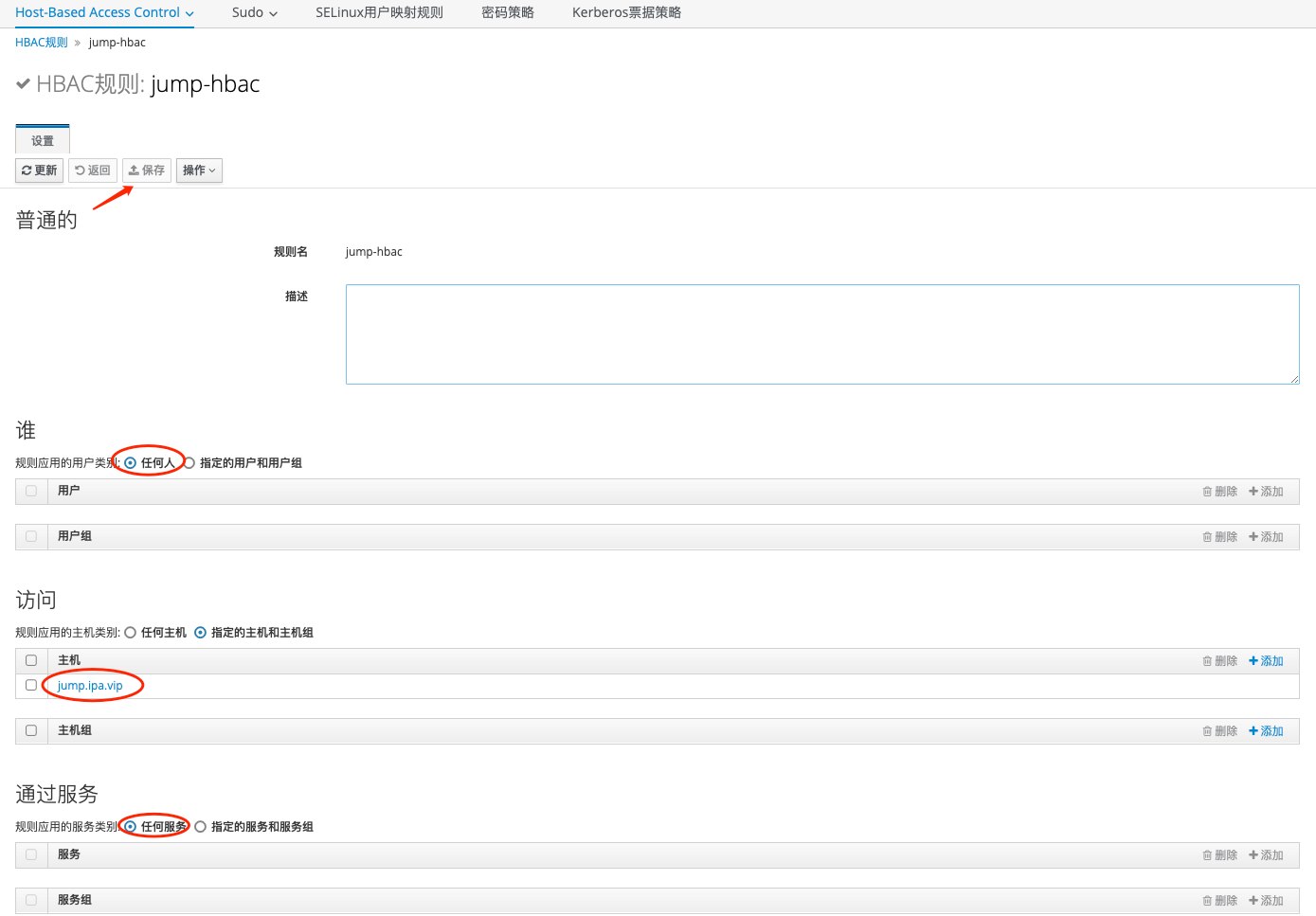
2、创建jump-hbac规则
允许所有账户可以登陆跳板机
HBAC规则-添加
| Bash |
|---|
| HBAC规则: jump-hbac
用户:任何人
主机:jump.ipa.vip
服务:任何服务
|
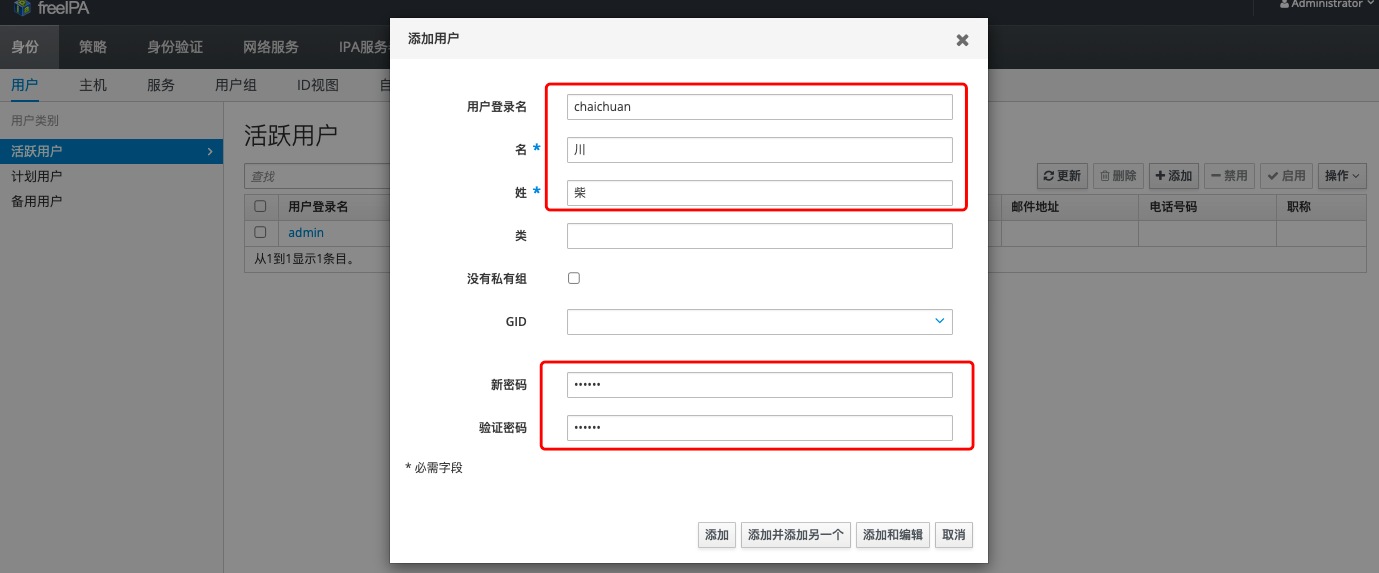
3、创建用户
身份-用户-活跃用户-添加
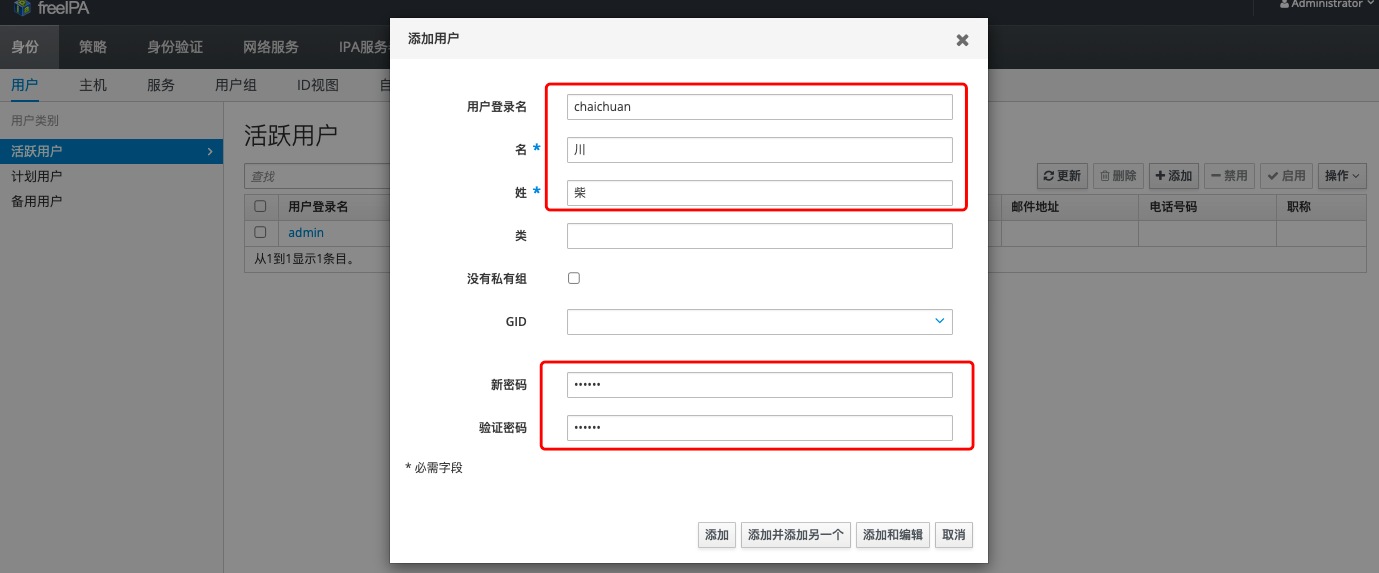
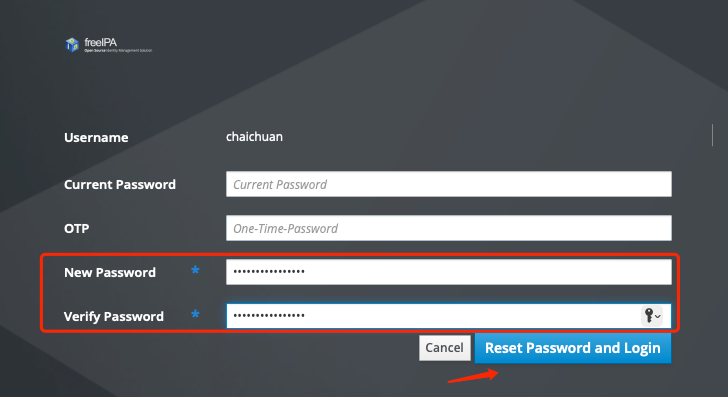
此时chaichuan用户已经有登陆堡垒机权限,但是需要先使用chaichuan用户登陆https://server.ipa.vip修改初始密码
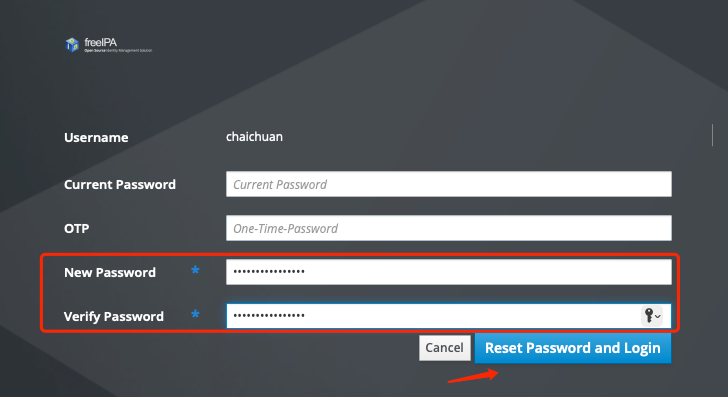
修改后可以测试跳板机的登陆
| Bash |
|---|
| $ ssh chaichuan@jump.ipa.vip
The authenticity of host 'jump.ipa.vip (172.26.32.53)' can't be established.
ED25519 key fingerprint is SHA256:Eoy2seoq4t0sB4nZF7AS2GrDxOHSiuP++j5xRCESx8Y.
This host key is known by the following other names/addresses:
~/.ssh/known_hosts:216: 172.26.32.53
Are you sure you want to continue connecting (yes/no/[fingerprint])? yes
Warning: Permanently added 'jump.ipa.vip' (ED25519) to the list of known hosts.
(chaichuan@jump.ipa.vip) Password:
Creating home directory for chaichuan.
jump.ipa.vip [~] 2025-07-14 17:13:02
# 执行jump 查看所属用户都有哪些主机权限,这时还没有添加主机,所以为空
chaichuan@pts/0 $ jump
Input:
==============================
$USER Host List:
==============================
SASL/GSSAPI authentication started
SASL username: chaichuan@IPA.TEST
SASL SSF: 256
SASL data security layer installed.
==============================
|
4、配置登陆主机权限
回到管理员页面,配置其他主机登陆权限
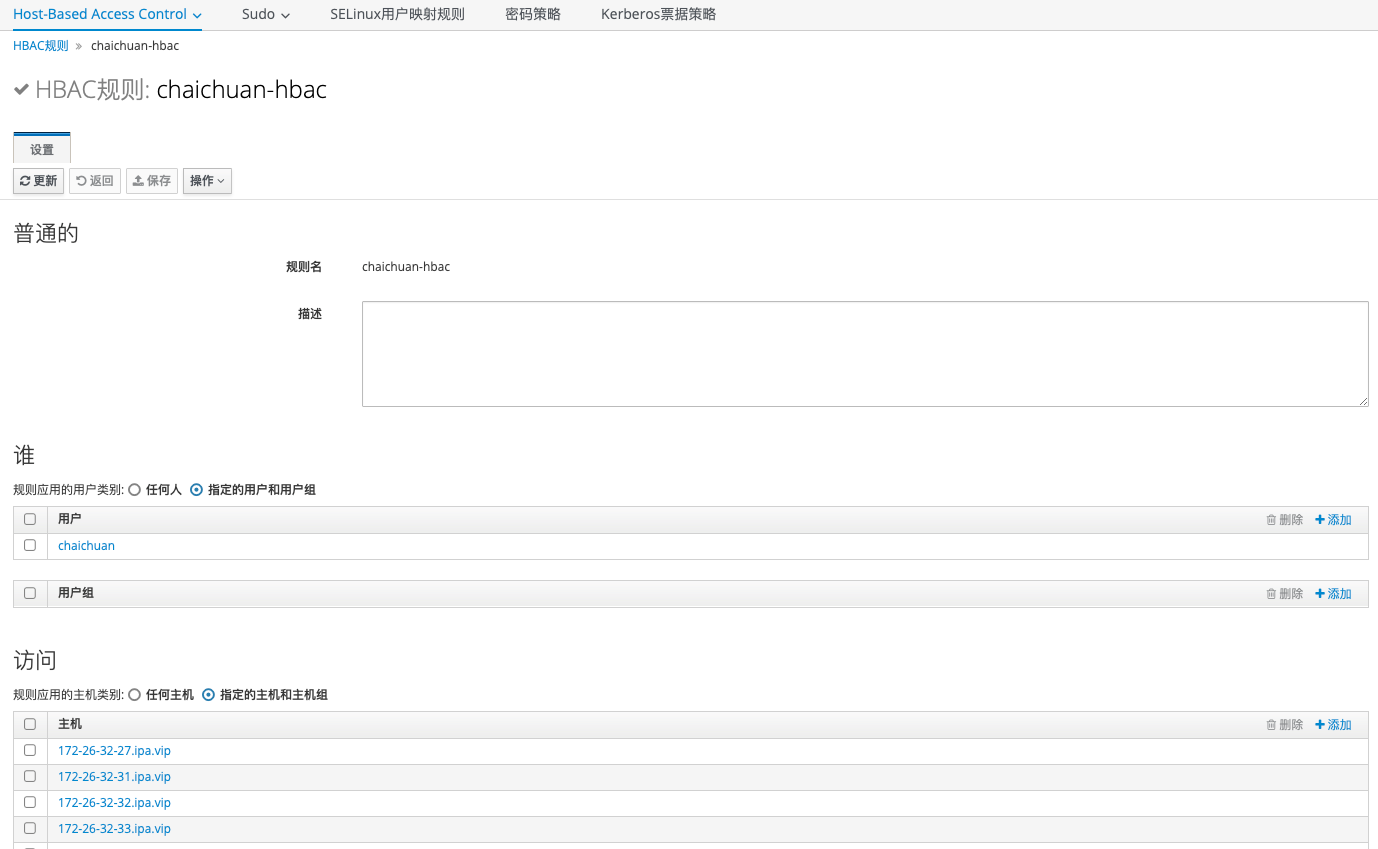
创建HBAC规则:chaichuan-hbac
| Bash |
|---|
| HBAC规则: chaichuan-hbac
# 此项需要选择创建的chaichuan用户
用户:chaichuan
# 此项选择需要的主机权限
主机:
172-26-32-27.ipa.vip
172-26-32-31.ipa.vip
...
服务:任何服务
|
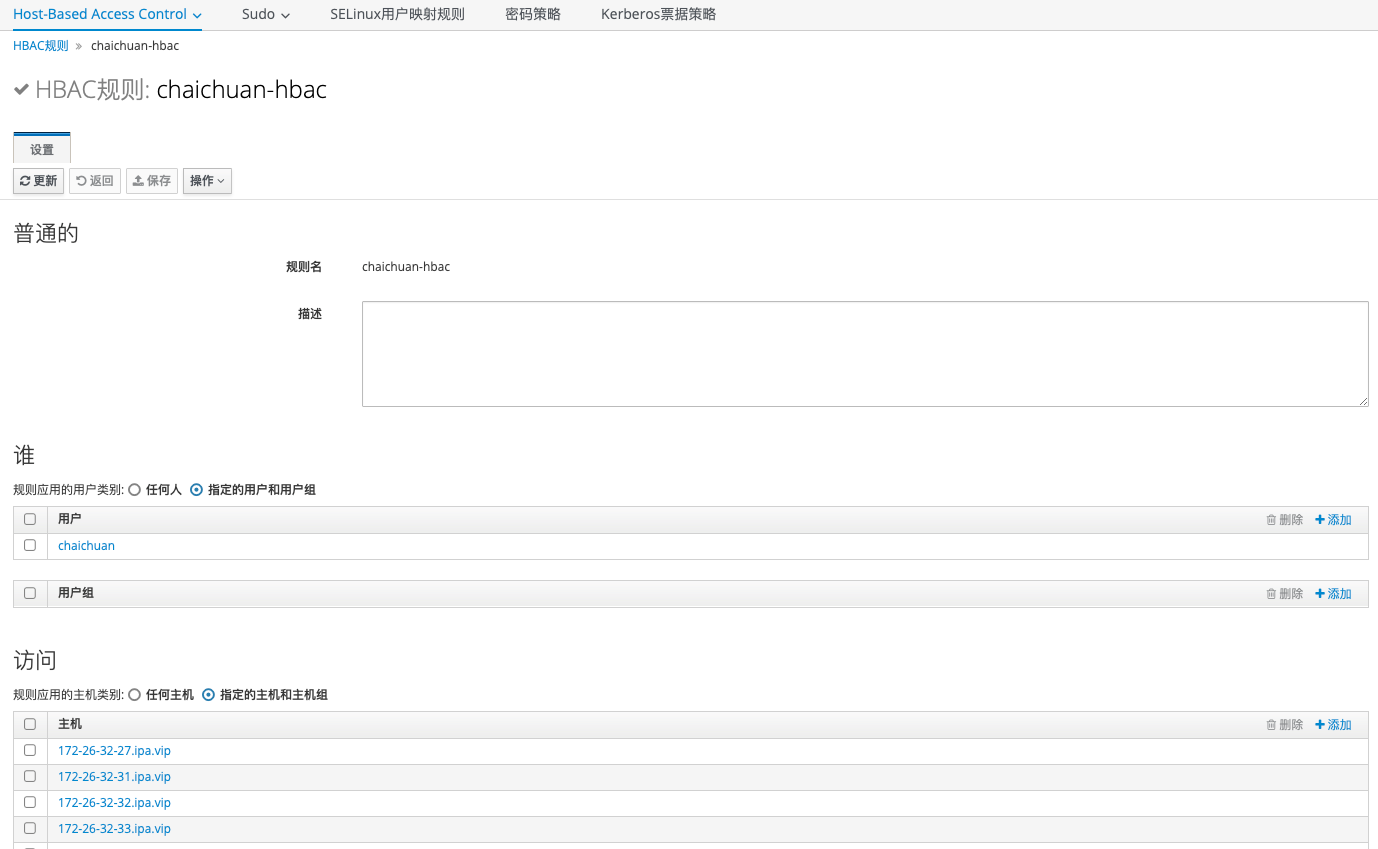
此时登陆跳板机可以看到配置的授权主机列表
| Bash |
|---|
| chaichuan@pts/3 $ jump #查看账户可以登陆的主机列表
Input:
==============================
chaichuan Host List:
==============================
SASL/GSSAPI authentication started
SASL username: chaichuan@IPA.VIP
SASL SSF: 256
SASL data security layer installed.
172-26-32-27.ipa.vip
172-26-32-31.ipa.vip
172-26-32-32.ipa.vip
...
# 登陆命令
chaichuan@pts/3 $ jump 27 #登陆172.26.32.27
Input: 27
SASL/GSSAPI authentication started
SASL username: chaichuan@IPA.VIP
SASL SSF: 256
SASL data security layer installed.
ssh 172-26-32-27.ipa.vip
Last login: Mon Jul 14 10:50:33 2025 from 172.26.32.53
Welcome to Alibaba Cloud Elastic Compute Service !
172-26-32-27.ipa.vip [~] 2025-07-14 17:44:50
chaichuan@pts/0 $
|
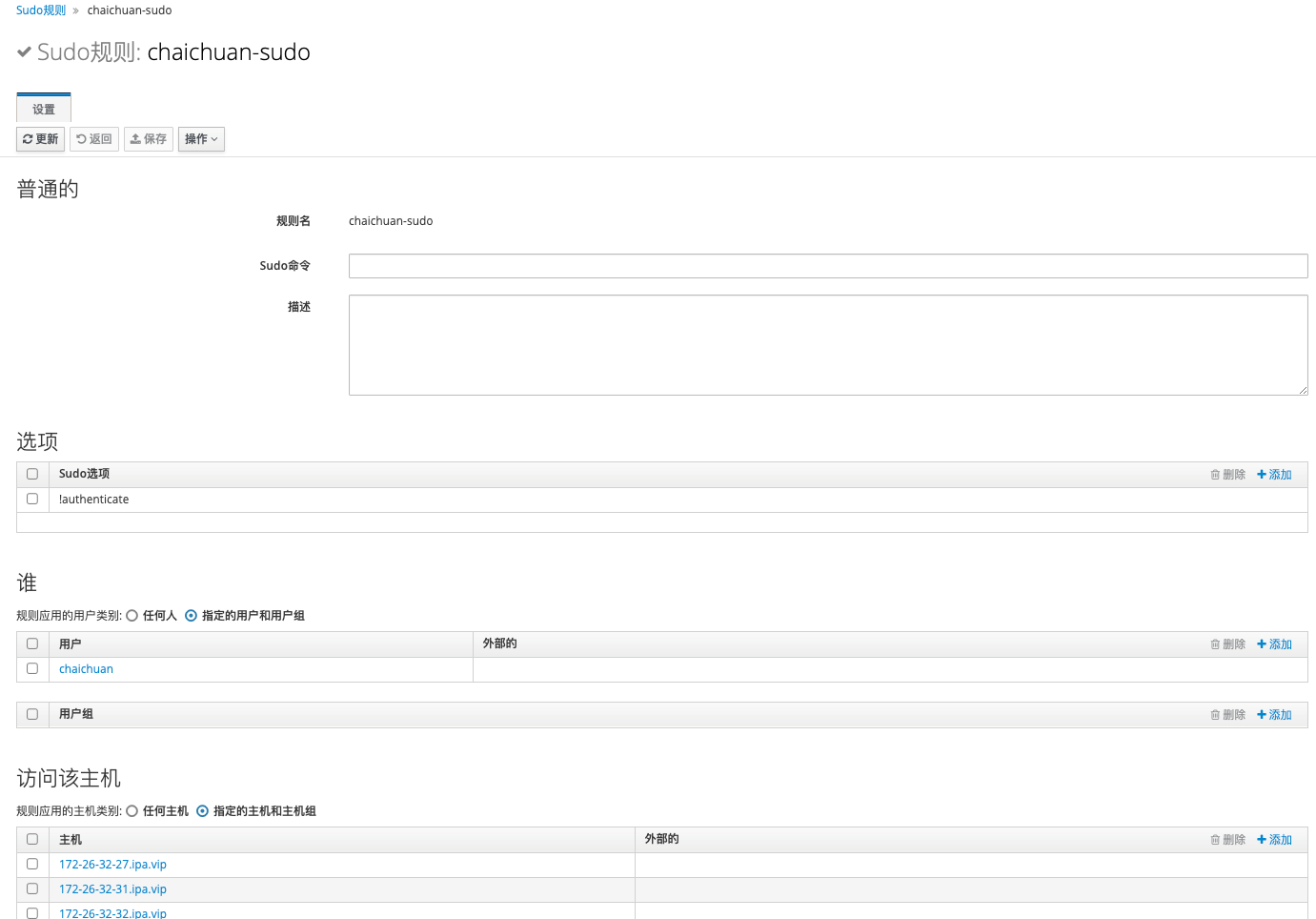
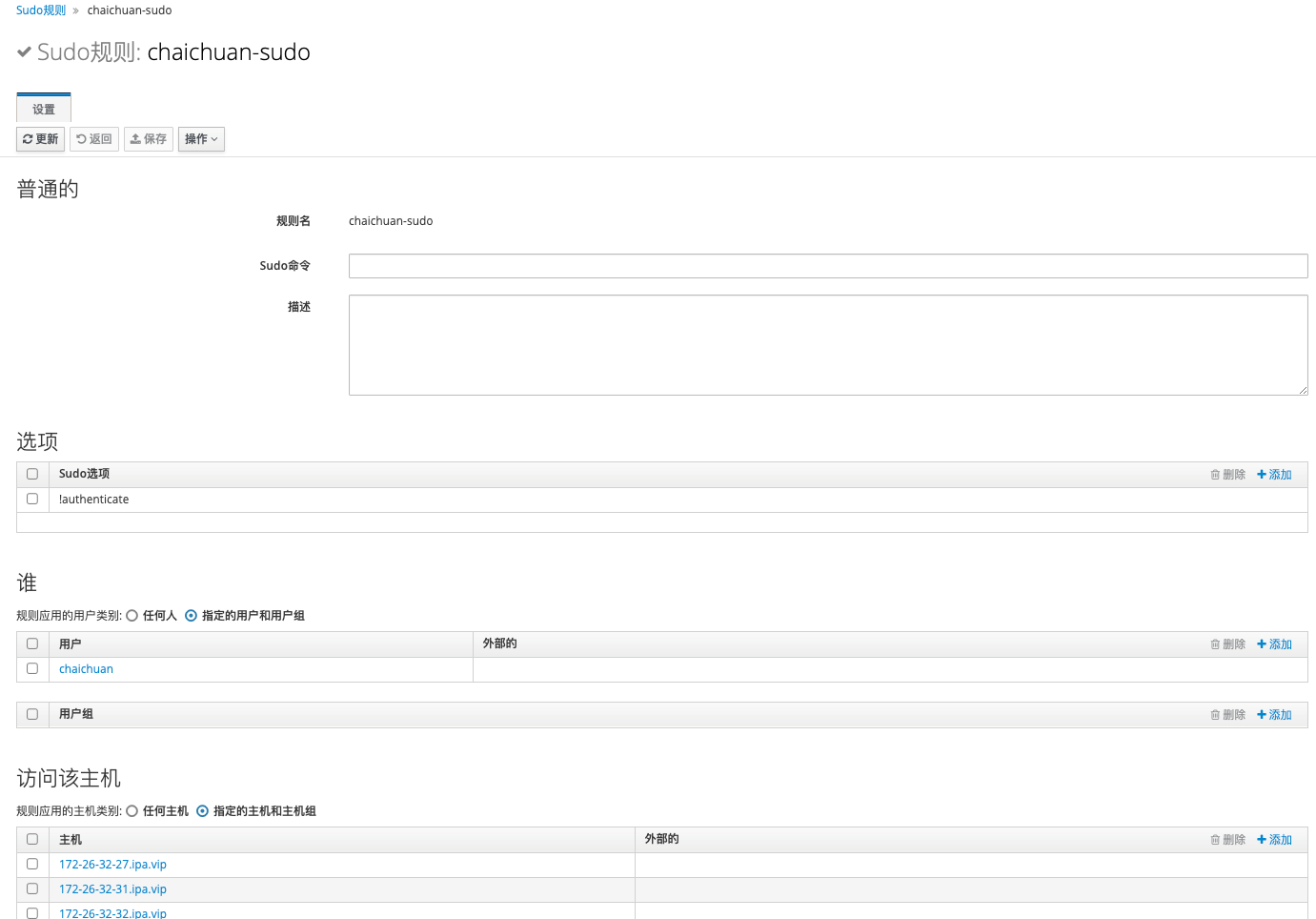
5、配置登陆主机后的sudo权限(可选)
创建 Sudo规则: chaichuan-sudo
| Bash |
|---|
| # 添加选项是为了再切换sudo时不需要再次输入账户密码
Sudo选项:!authenticate
# 此项需要选择创建的chaichuan用户
用户:chaichuan
# 此项选择需要的主机sudo权限
主机:
172-26-32-27.ipa.vip
172-26-32-31.ipa.vip
...
# 这里配置任何命令,也可以指定,比如sudo cat /etc/shadow
允许命令:任何命令
|
测试切换root权限
| Bash |
|---|
| 172-26-32-27.ipa.vip [~] 2025-07-14 17:58:52
# 使用sudo -i 直接切换root用户
chaichuan@pts/0 $ sudo -i
# 或者使用sudo cat /etc/shadow 直接执行命令
chaichuan@pts/0 $ sudo cat /etc/shadow
root:$6$lMd2Puho$0.39vuWh9G44Yy6nE/elLW6xIETvj.231yV3hdHp3tjndBYo0ejf3yMqVJYlxJ5YDYX6wOsrqmDuKXVX5/1MP.:20162:0:99999:7:::
bin:*:17246:0:99999:7:::
daemon:*:17246:0:99999:7:::
adm:*:17246:0:99999:7:::
lp:*:17246:0:99999:7:::
sync:*:17246:0:99999:7:::
shutdown:*:17246:0:99999:7:::
......
|